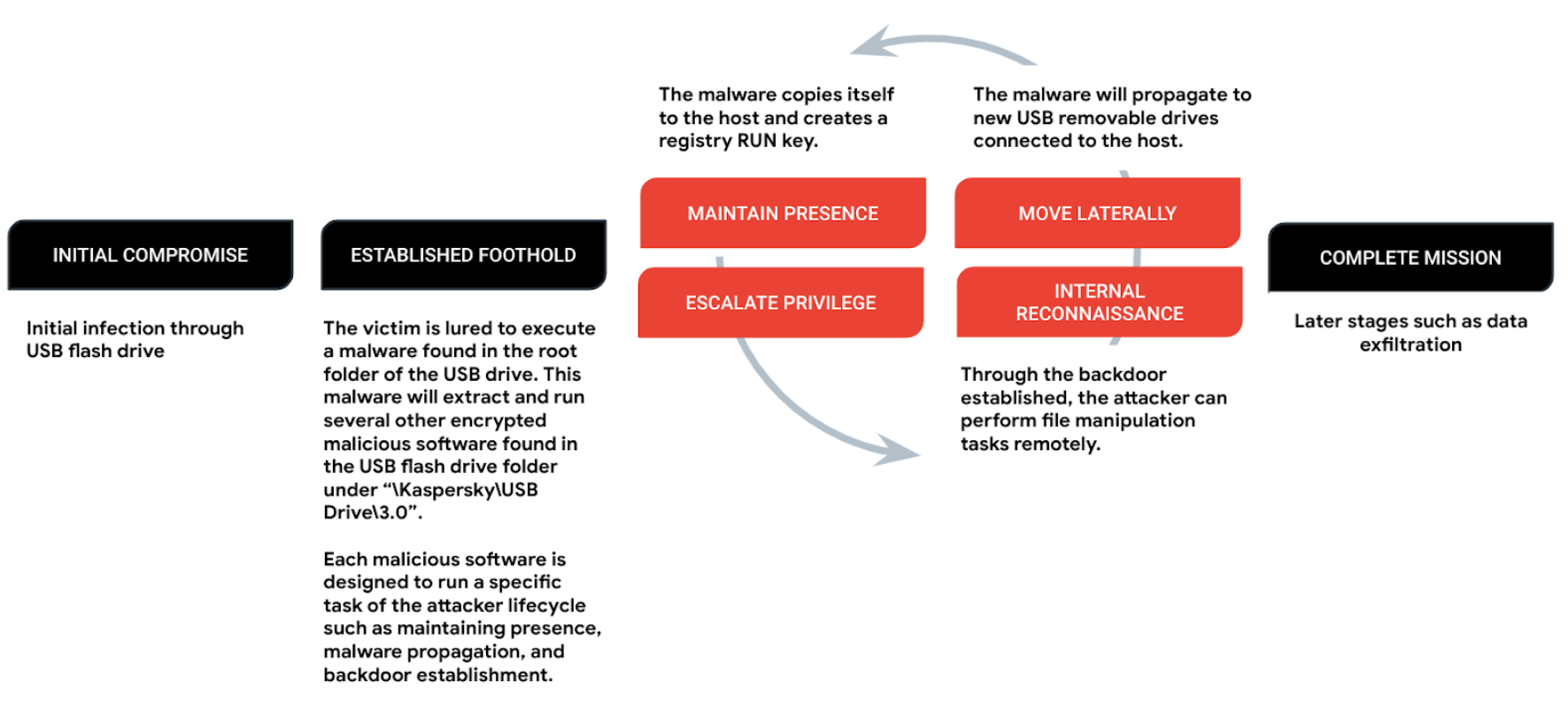
Stealthy USB: New versions of Chinese espionage malware propagating through USB devices found by Check Point Research - Check Point Blog

Amazon.com: Yubico YubiKey 5C - Two Factor Authentication USB Security Key, Fits USB-C Ports - Protect Your Online Accounts with More Than a Password, FIDO Certified : Electronics

Amazon.com: Yubico YubiKey 5C - Two Factor Authentication USB Security Key, Fits USB-C Ports - Protect Your Online Accounts with More Than a Password, FIDO Certified : Electronics

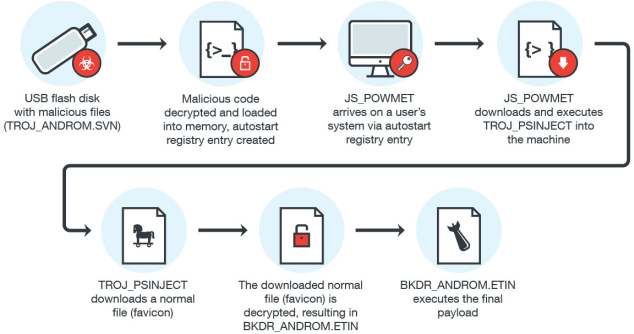
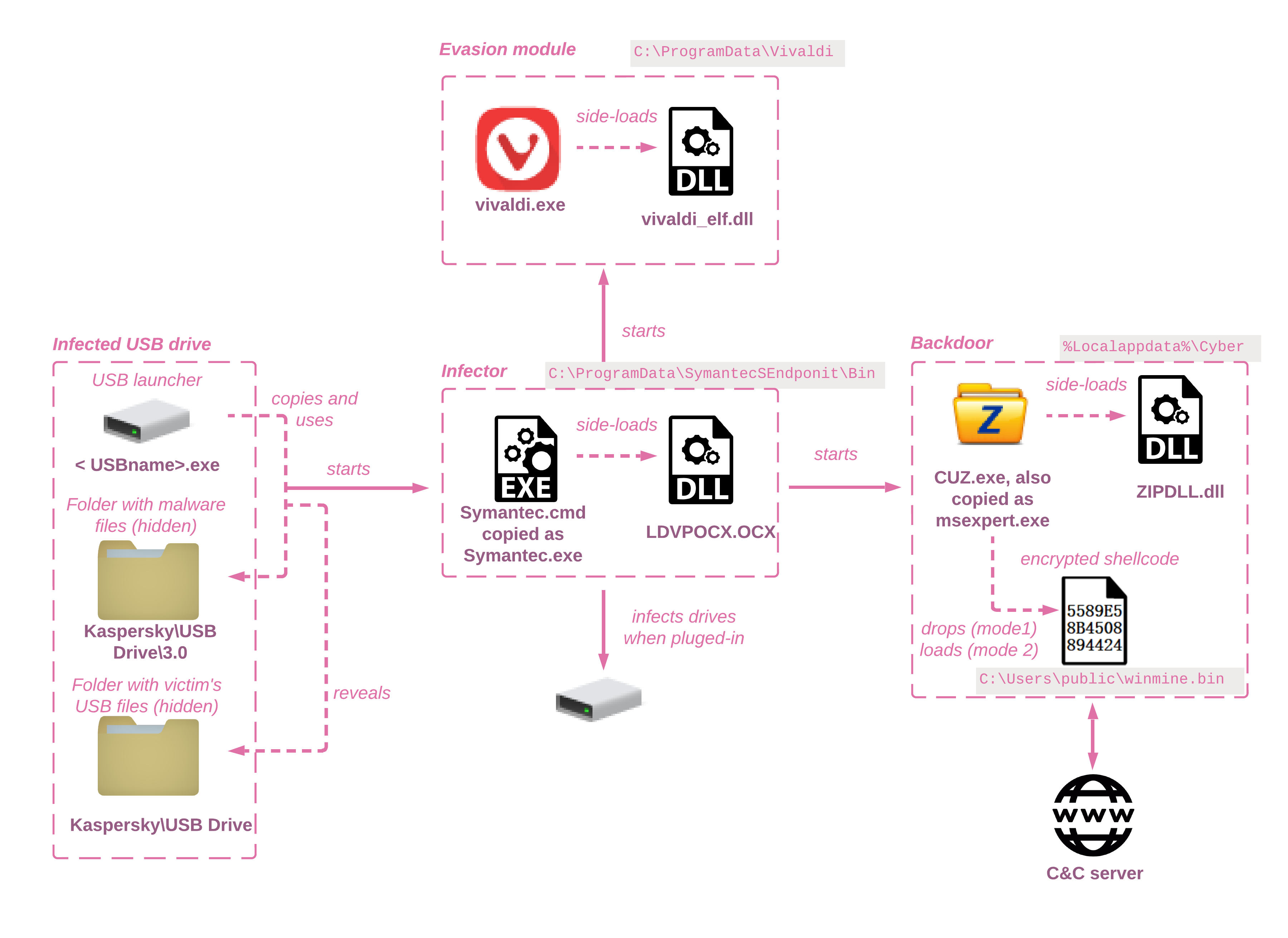
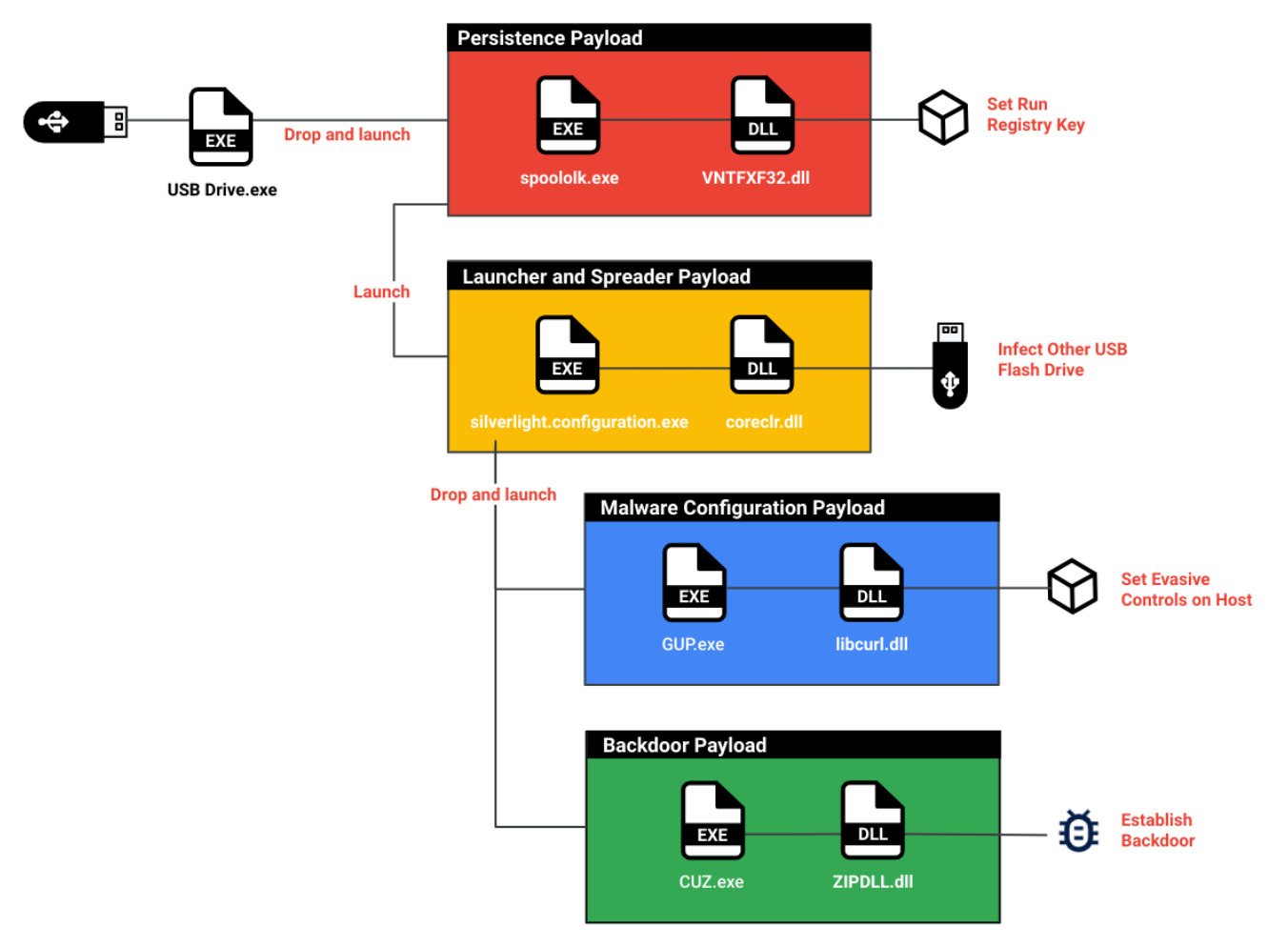
Mandiant details UNC4191 cyber espionage activity using USB devices as initial infection vector - Industrial Cyber
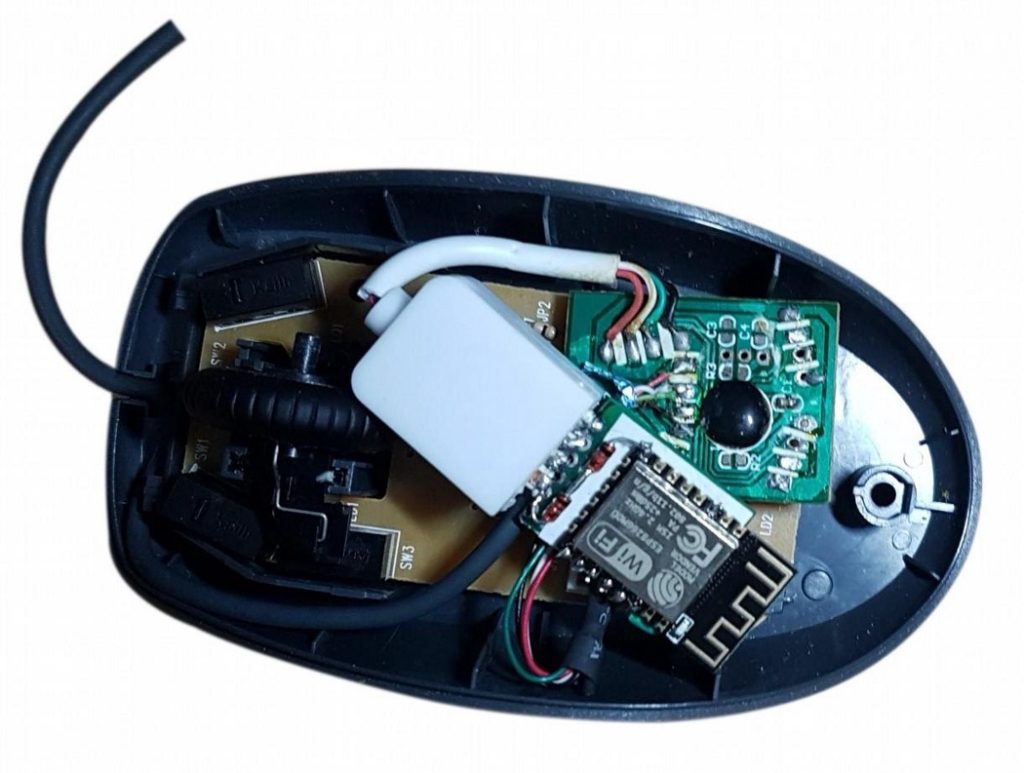
Evil Maid" Firmware Attacks Using USB Debug - Eclypsium | Supply Chain Security for the Modern Enterprise